Take online information with big grain of salt

Investigations by Taifa Leo showed that some of the photos used were from long ago and cannot be whatsoever linked to the riots.
The internet is a vast repository of information. The content on the web contains some accurate information, reliable sources, and useful resources, but it also contains a lot of misleading information, propaganda, and made-up or biased information.
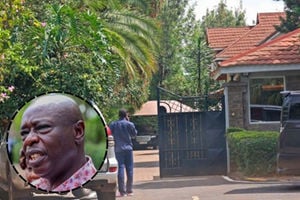
Recently, the Directorate of Criminal Investigations, or DCI, published false images of people who were allegedly involved in the ongoing protest marches. Some of the photos were over 10 years old, and some of them weren't even taken in Kenya. The DCI had demanded that anyone whose image had been published show up at the local police station to assist with the investigation.
Because of how embarrassing this error was, the DCI had to apologise. So, it begs the question: What procedures does the DCI employ to gather and verify information for prosecution? Could this error be the proverbial canary in the coal mine, indicating why the agency rarely sustains high-profile, major crime cases?
Confusion
While the DCI is the most visible offender in this case, many organizations are struggling to manage the jets of information that, in the absence of structures and guardrails, can result in errors, some of which can be egregious.
Such information may spread false or deceptive information, resulting in misunderstandings, confusion, and poor decisions. It may cause the public to lose faith in the person or group spreading it. It might result in legal action. Individuals may suffer irreparable physical or reputational harm due to the publication of inaccurate information about them.
Anyone can contribute information to the internet, regardless of their credentials, level of expertise, or motivation. This implies that a wide range of viewpoints, beliefs, and opinions may be presented online, some of which might not be supported by solid data or research.
Dubious information
DCI and other organisations must recognise and inventory trustworthy information sources in order to guard against harvesting dubious information. These sources may include reputable news organisations, governmental bodies, educational institutions, and subject-matter specialists. Using social media exclusively is not only pointless but also ridiculous.
It's crucial to have a process and policy in place to confirm the accuracy of the information. Checking information sources' credentials, knowledge, and track record can help. It also entails talking to their peers, looking over the source's other works that have been published, and running background checks.
The DCI should institutionalise information sharing by creating policies for sharing information with other agencies and organisations. To avoid leaks that could jeopardise the security of sources, however, this strategy would necessitate agreements on procedures for protecting sensitive information among the cooperating agencies. In particular, there is a need to strengthen and elevate human intelligence through the hiring and training of human intelligence sources.
Mr. Wambugu is an accredited expert in cloud and cyber security. Email: [email protected] Twitter: @Samwambugu2